Audit-Ready by Default - 4 Mechanical Guarantees, No Add-Ons
These controls are not configuration options - they are built into every transaction, every document, and every login in Naologic. Finance teams and IT Directors get complete forensic coverage without purchasing a separate compliance module.
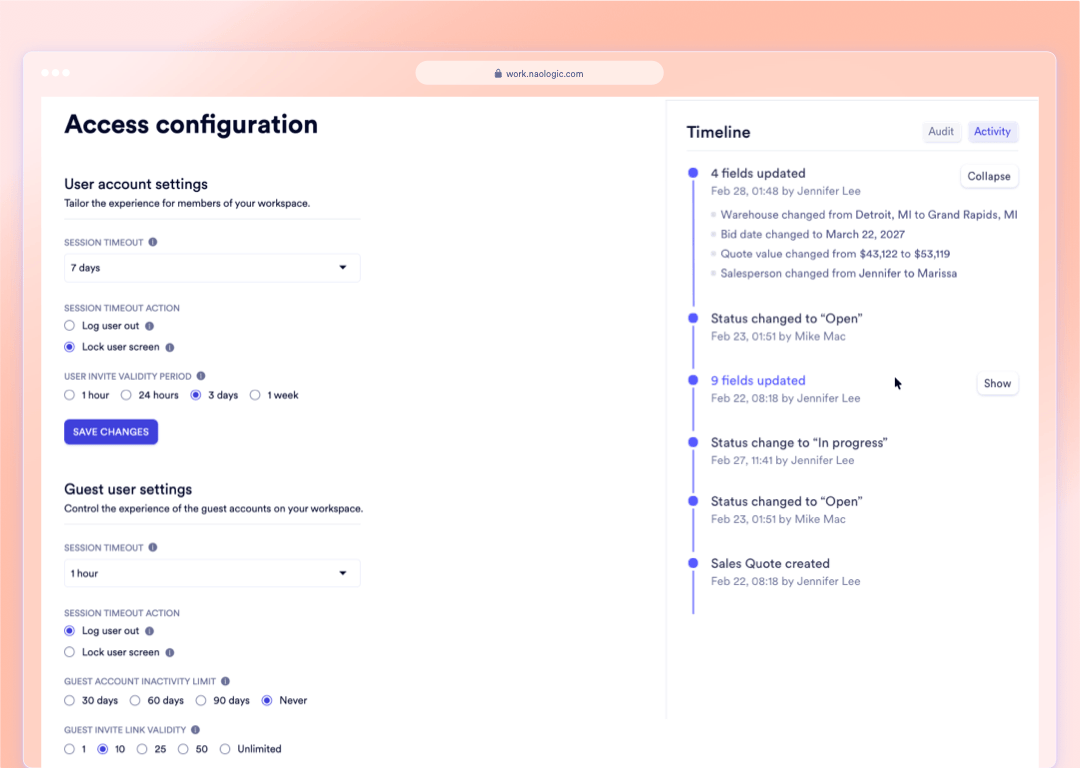
Every Document, Every Edit, Traceable to the Exact Second
Every order, invoice, and journal entry in Naologic carries a permanent, immutable audit log that records exactly which user changed which data field - including the previous value, the new value, and the UTC timestamp. Toggle between a human-readable activity feed for routine review and a raw JSON state export for external auditors or forensic investigations.
Financial Access Controls
4 Granular Firewalls Protecting Your General Ledger
Basic ERPs bundle financial permissions together - the user who drafts invoices may also have the ability to adjust tax rates or reconcile your bank accounts. Naologic decouples them: posting rights, reconciliation rights, template execution rights, and legal tax identifiers are each independently controlled.
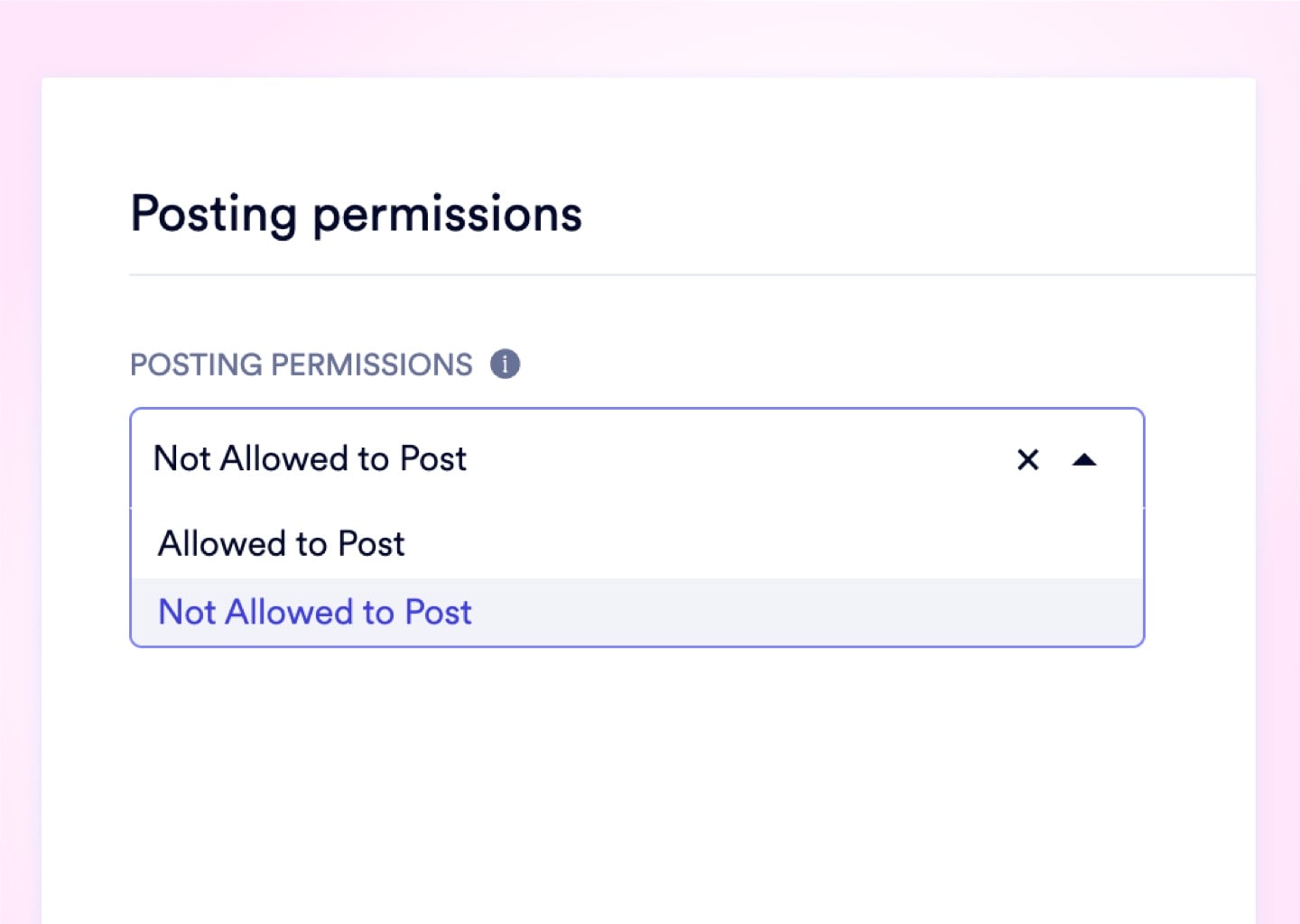
Custom Posting Permissions
Designate parent GL accounts as Header Accounts to physically prevent users from posting transactions to broad roll-up categories. Every journal entry is forced to the correct, granular sub-account - eliminating the accidental $10,000 mispost that ruins department budget tracking.
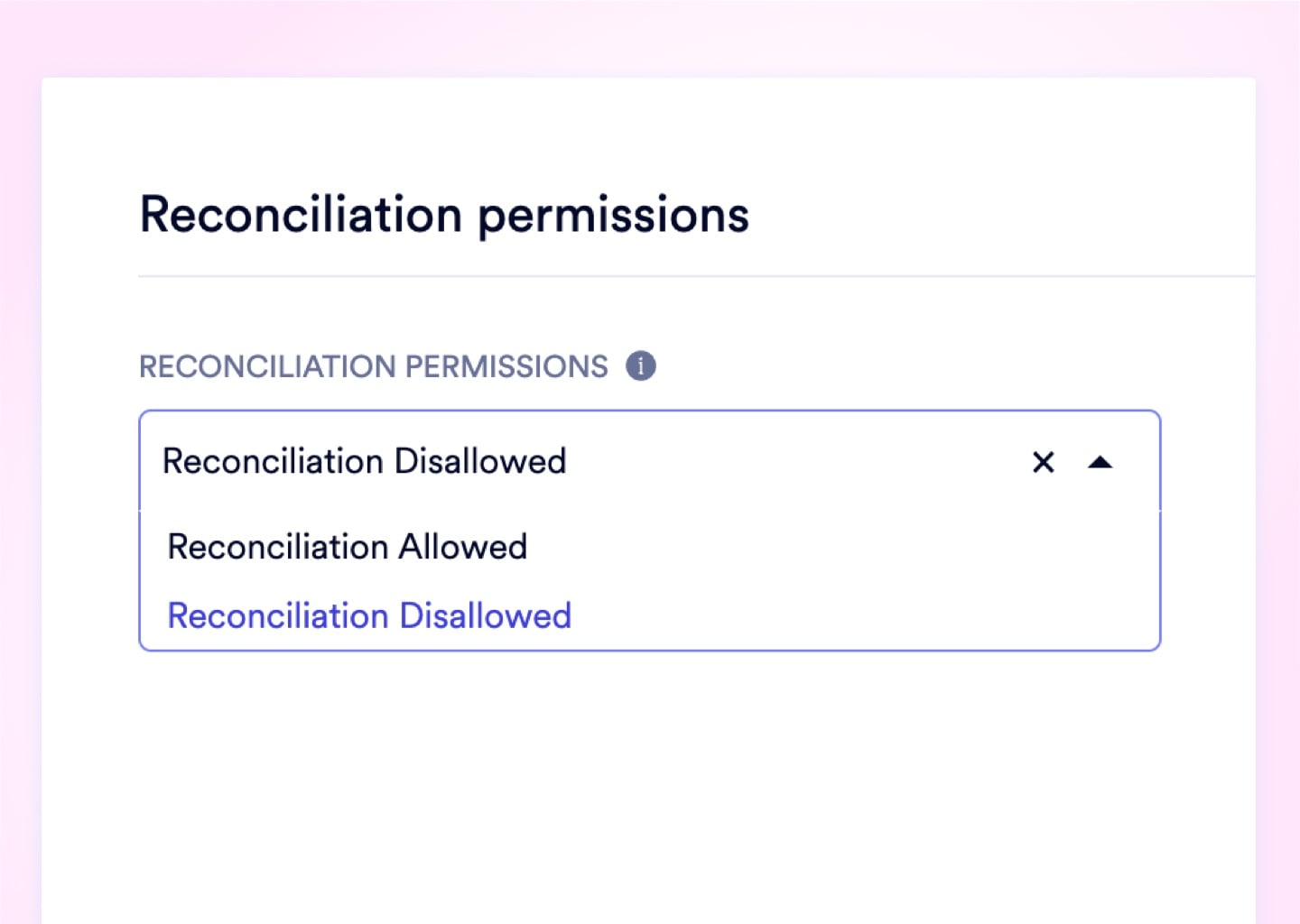
Reconciliation Permissions
Set per-account reconciliation rules to completely exclude internal clearing ledgers and depreciation accounts from your bank feed. Only cash-relevant GL activity surfaces in the month-end reconciliation workspace - zero noise, zero confusion.
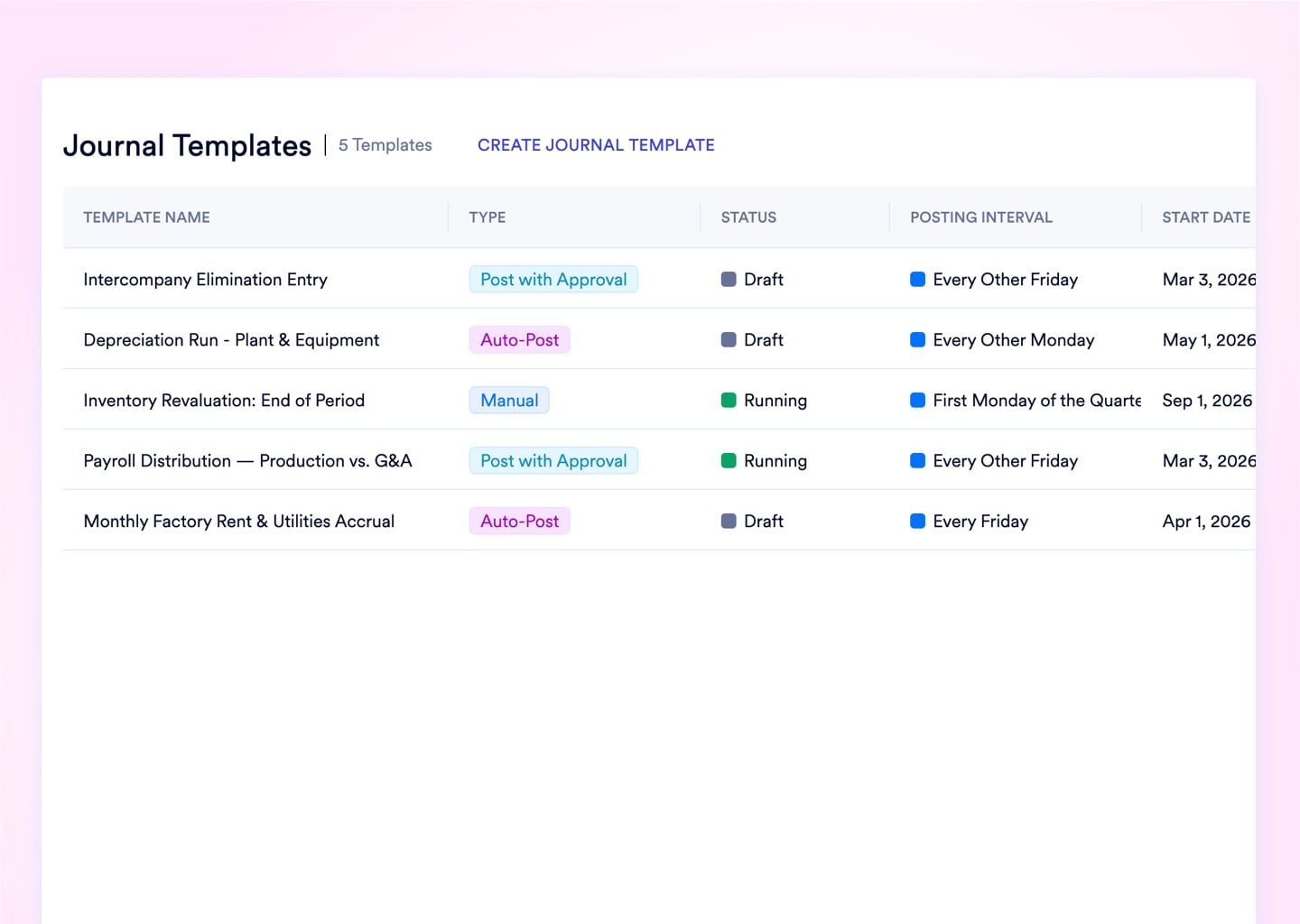
Journal Template Posting Permissions
Choose auto-post, draft-for-approval, or manual review independently for each recurring journal template. Fixed expenses like rent auto-post; variable entries like utilities route to a draft queue for human sign-off before hitting the ledger.
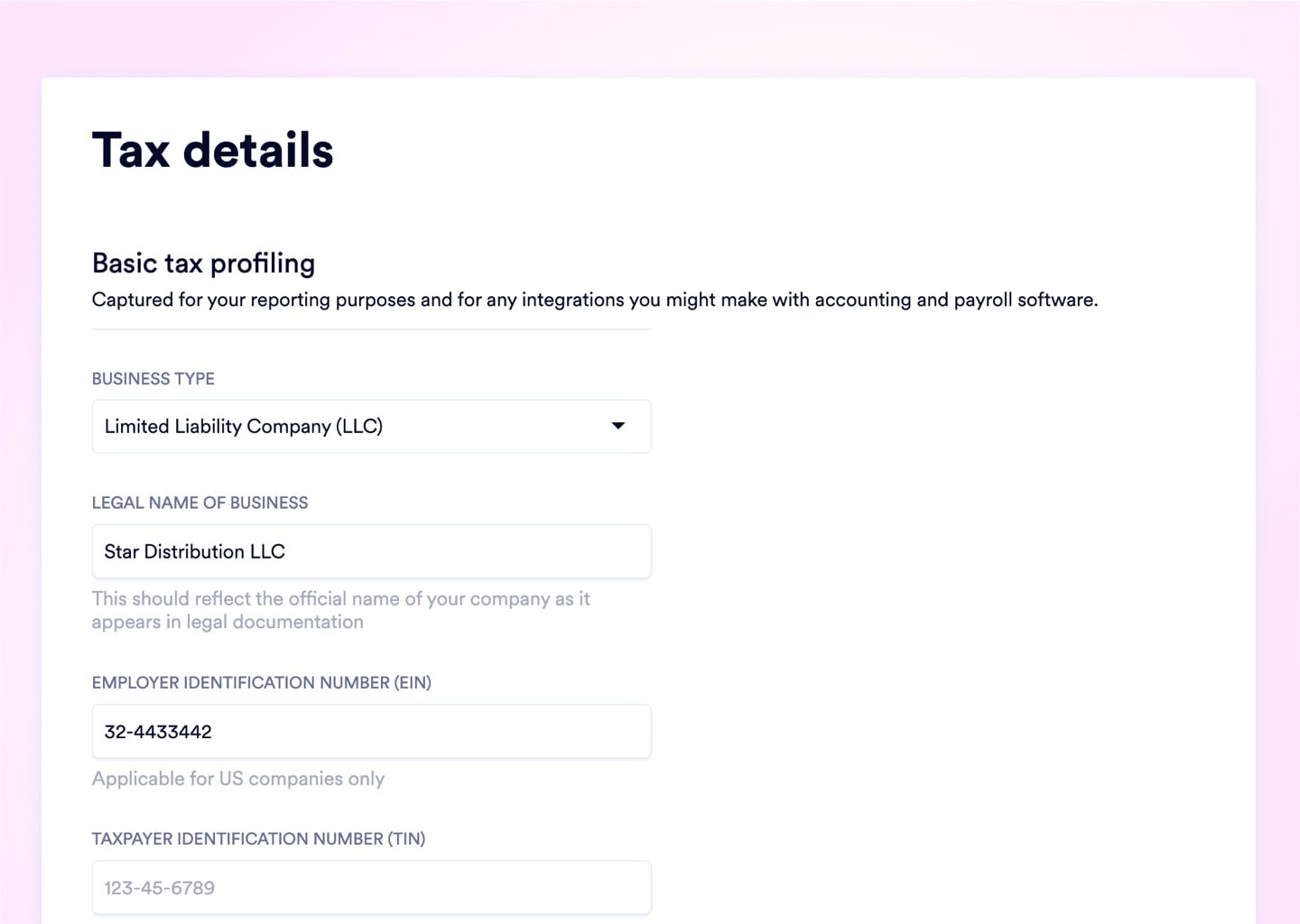
Tax Settings
Store your exact legal entity name, EIN, and Taxpayer IDs in a secure registry that auto-populates IRS forms, customs declarations, and compliance reports. No manual data retrieval required every time a regulatory document is generated.
Every $14,000 COGS Entry Traced Back to Its Goods Receipt in 1 Click
When an auditor demands justification for a specific journal entry, Naologic provides a direct, clickable hyperlink embedded inside every automated entry that opens the exact source document - the shipping receipt, sales order, or invoice - that triggered it. Stop spending hours digging through paper files to justify what the ledger recorded; the answer lives inside the entry itself.
4 Controls That Close External and Internal Access Vectors
Enterprise Roles with CRUD Controls
Build hyper-granular permission matrices with Create, Read, Update, Delete rights down to the individual document and geographic warehouse level. Replace the dangerous binary of "Admin vs. User" with airtight role boundaries that stop unauthorized financial postings before they happen.
- Per-document CRUD permission matrix
- Geographic and departmental access limits
- Ownership scoping - own documents only
- Business unit data segregation
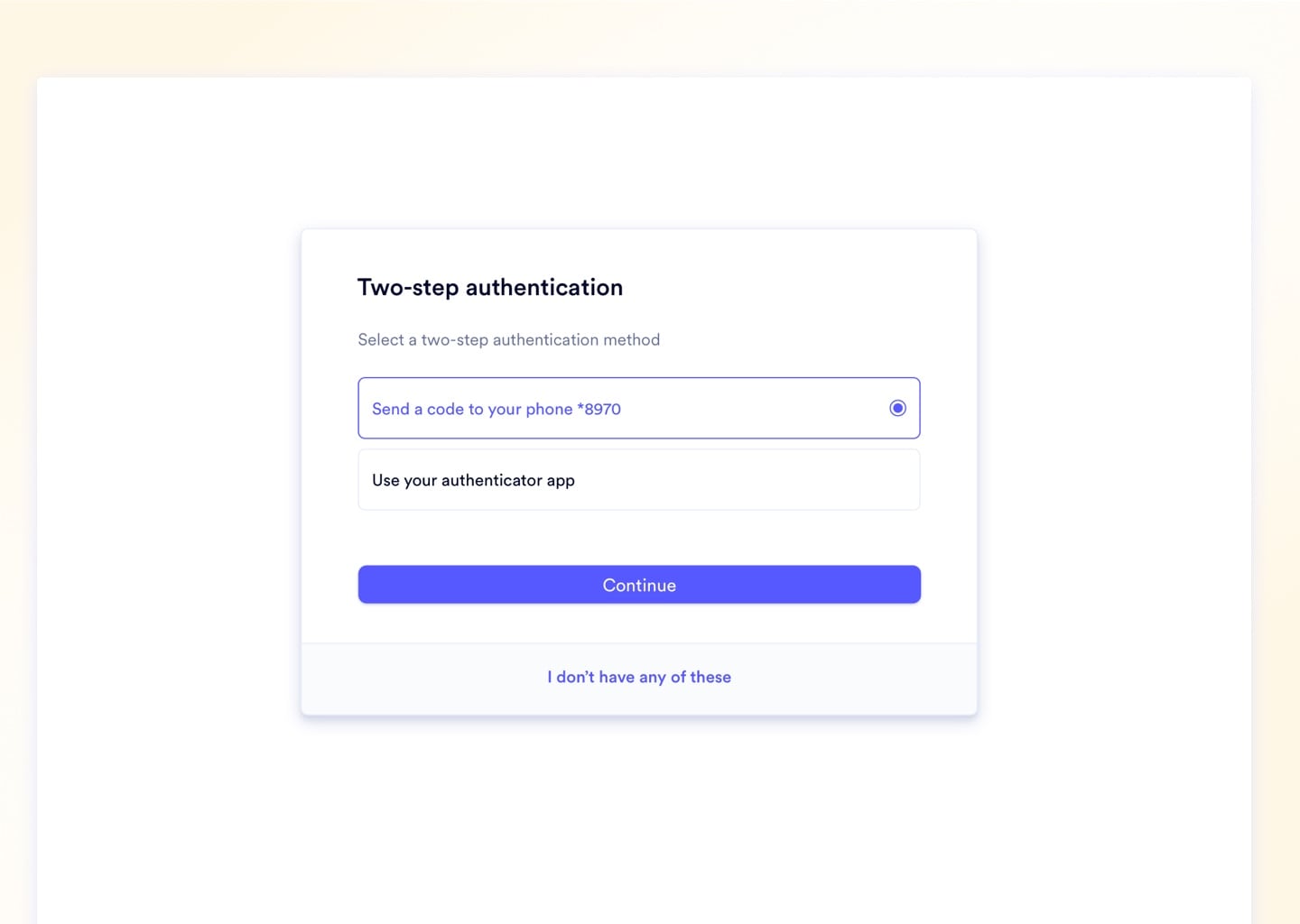
Mandatory 2-Factor Authentication
Super Admins toggle a single global enforcement switch to intercept any user who attempts to log in without a linked TOTP authenticator or verified SMS number. A single compromised password can no longer unlock your corporate bank data or financial records.
- SMS and Authenticator App (TOTP) support
- Global enforcement toggle for all seats
- Per-user 2FA compliance monitoring
- Admin-forced 2FA setup on next login
Guest User Session Controls
External auditors and contractors receive restricted Guest roles with auto-expiring session links - eliminating the forgotten-credential vulnerability that leaves active ERP credentials in the wild for months. Aggressive inactivity limits terminate guest sessions automatically after a configurable idle period.
- Auto-expiring guest login links
- Dedicated guest role with limited scope
- Separate inactivity threshold from employees
- No additional enterprise seat license required
Scoped REST API Tokens
Generate Read, Write, or Full Access scoped Bearer Tokens for each external integration - eliminating shared master credentials entirely. Every token is independently revocable from the Developer Settings panel with zero impact on other active connections.
- Read / Write / Full Access scoping per token
- Independently revocable per integration
- Auto-generated Swagger API documentation
- Open REST architecture - no data trapped behind walled gardens
Session Security
Force Every Idle Terminal to Lock or Log Out on a Configurable Timer
An unattended workstation on the factory floor is an open door into your financial data - configure precise session timeout windows, define whether idle screens lock behind a PIN or terminate the session entirely, and set exact expiration windows for new user invitation links from 1 hour to 1 week. Access configuration enforces these policies globally across every seat in the workspace without requiring IT involvement.

Compliance Outcomes
4 Measurable Results From Replacing Manual Compliance Processes
Manual compliance workflows - shared admin passwords, exported Excel audit logs, undifferentiated permission tiers - create vulnerabilities that surface at the worst possible time. These are the specific, mechanical outcomes of closing those gaps inside Naologic.
1 click
to answer any source document audit question - every automated journal entry resolves directly to the goods receipt, sales order, or invoice that triggered it
3
independent financial permission layers separated by default: custom posting controls, per-account reconciliation rules, and journal template execution policies
0
additional seat licenses required for external auditors - Guest Users receive restricted, scoped access with auto-expiring credentials at no extra cost
10
single-use cryptographic recovery codes generated per 2FA setup, ensuring locked-out executives can restore access without disabling the policy
Full Feature Reference
15 Security Controls Across 5 Compliance Categories
The complete Naologic security and compliance stack, organized by function for technical evaluation. Each control listed here maps to a specific system behavior - not a configuration recommendation or a paid add-on.