Access Control That Matches Your Org Chart
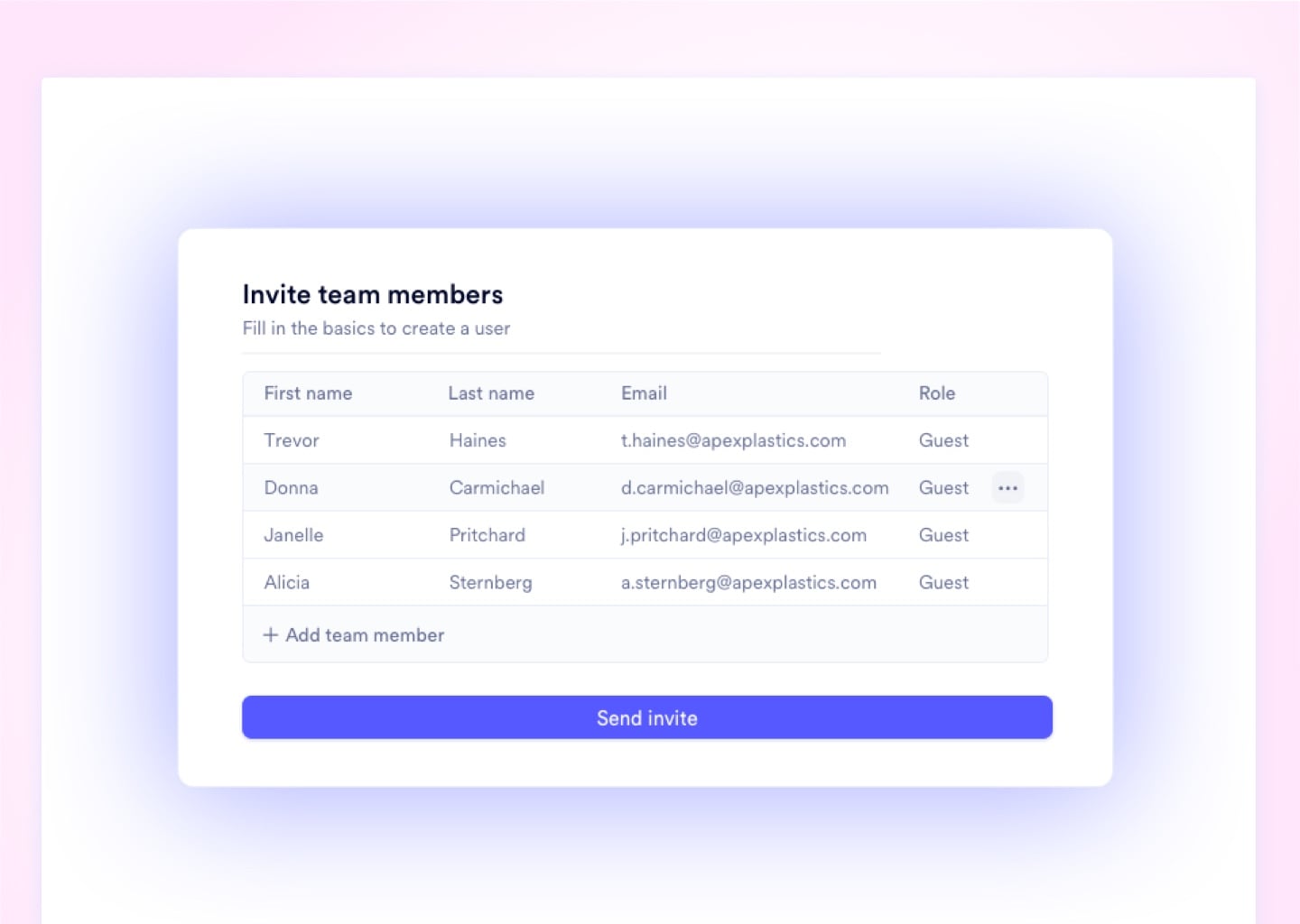
Provision a compliant user seat in under 2 minutes
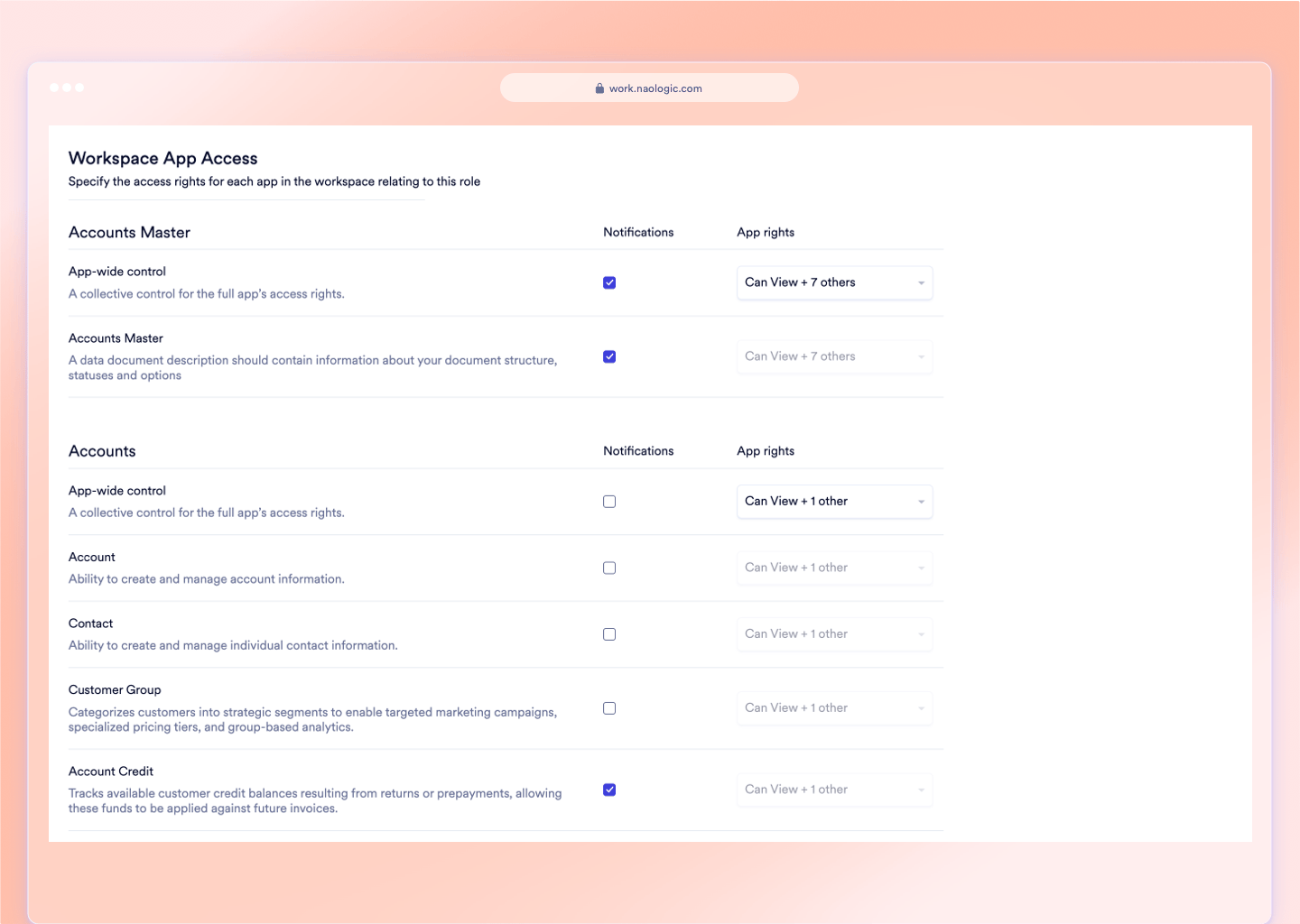
Manufacturing operations run on trust hierarchies. A plant manager in Ohio should never see the Dallas division's margin data, and a 3PL contractor should never access your GL. Naologic enforces those real-world boundaries digitally. Every permission is configurable through a visual admin console - zero database coding, zero IT tickets, zero consulting fees. You define the access architecture. The system enforces it automatically across every module, every user, and every terminal on your floor.
< 2 min
Average time to provision, update, or revoke a user seat - vs. 3-day IT ticket queues in legacy ERPs
$0
Cost of a Guest User seat for external auditors or 3PL contractors - vs. full enterprise license fees in NetSuite or SAP
14
Distinct CRUD permission layers per module - Create, Read, Update, Delete configured down to the individual document type
100%
Document coverage in Naologic's audit trail system - every order, invoice, and transaction carries an immutable log of every user action
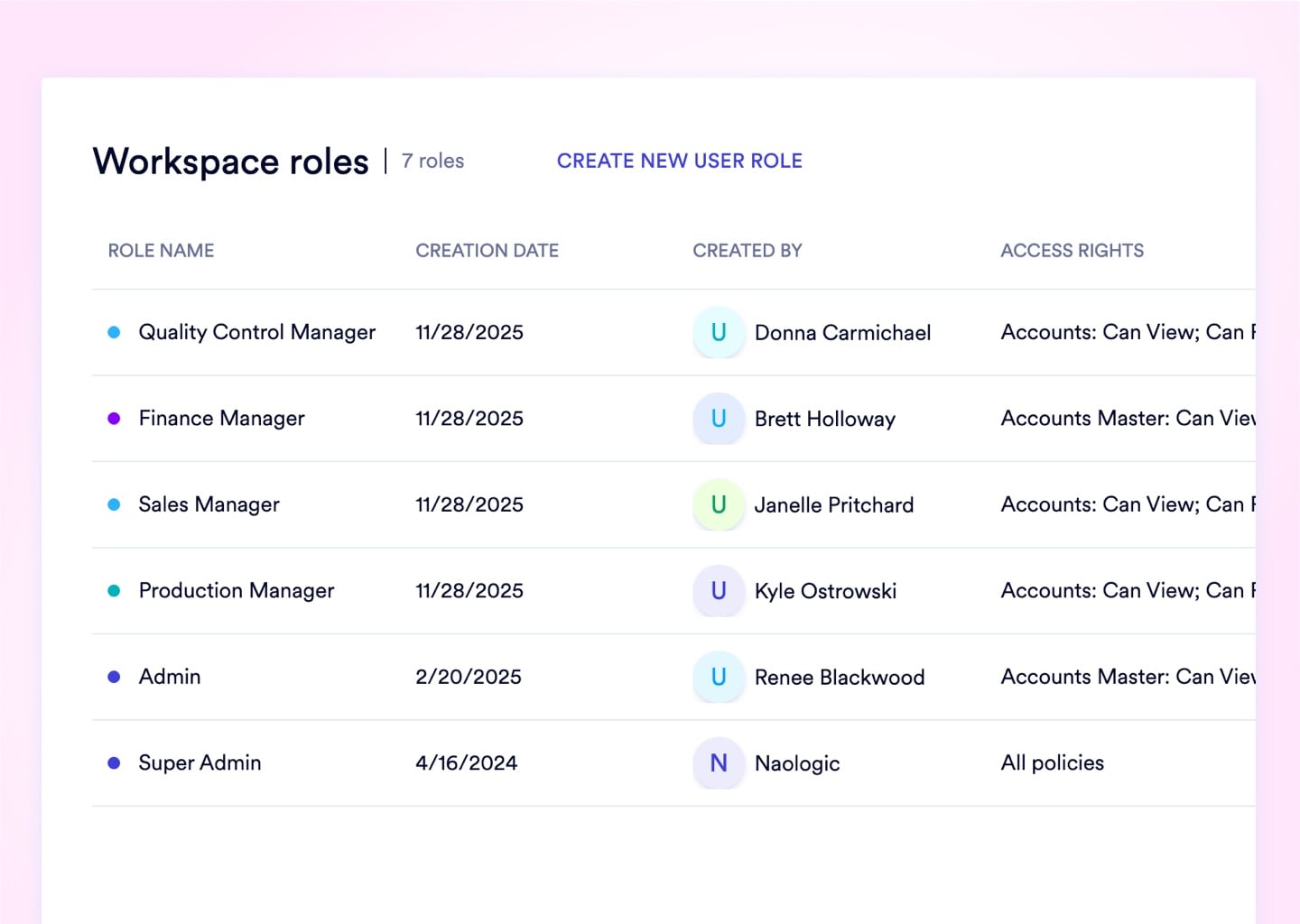
4 Permission Mechanisms Protecting Your Data
Document-Level CRUD Permissions
Set explicit Create, Read, Update, and Delete rights per user, per module, and per document type. Eliminate the Admin-vs-User binary that forces dangerous access trade-offs with junior staff and financial data.
- Custom roles down to individual document type
- Geographic and departmental permission scoping
- "Own Documents Only" ownership enforcement
- Module-level CRUD matrices per job function
- Zero-code configuration via visual admin UI
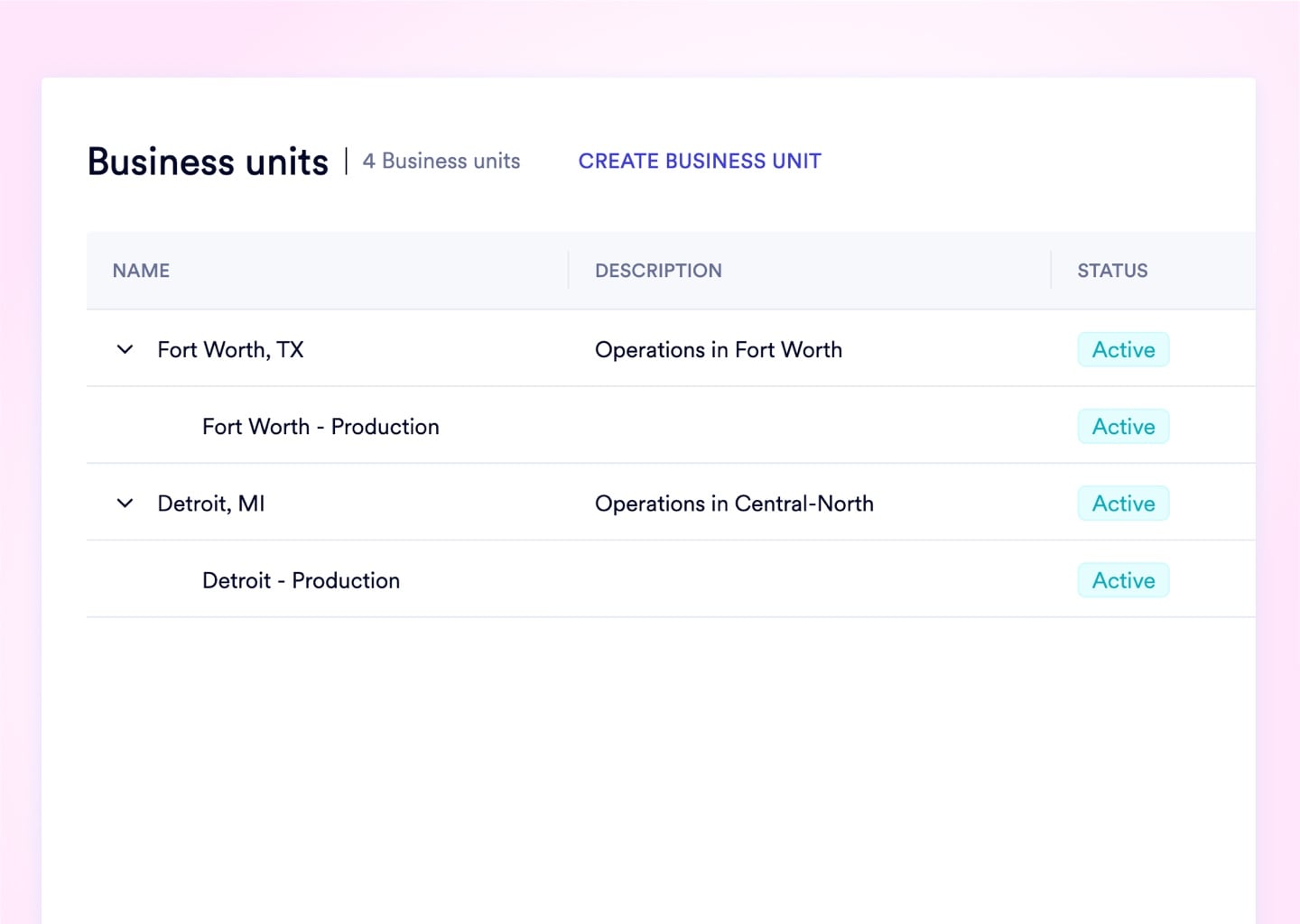
Geographic Data Compartmentalization
Segregate inventory, sales, and financial data by region or subsidiary within one unified workspace. A Dallas branch manager cannot see EMEA margin data - and the system structurally enforces that boundary.
- Named Business Units by geography or department
- Hard visibility filters applied at role assignment
- Eliminates the need for separate ERP instances per division
- Global data centrally reportable to executives
- Business Unit tags applied at user provisioning
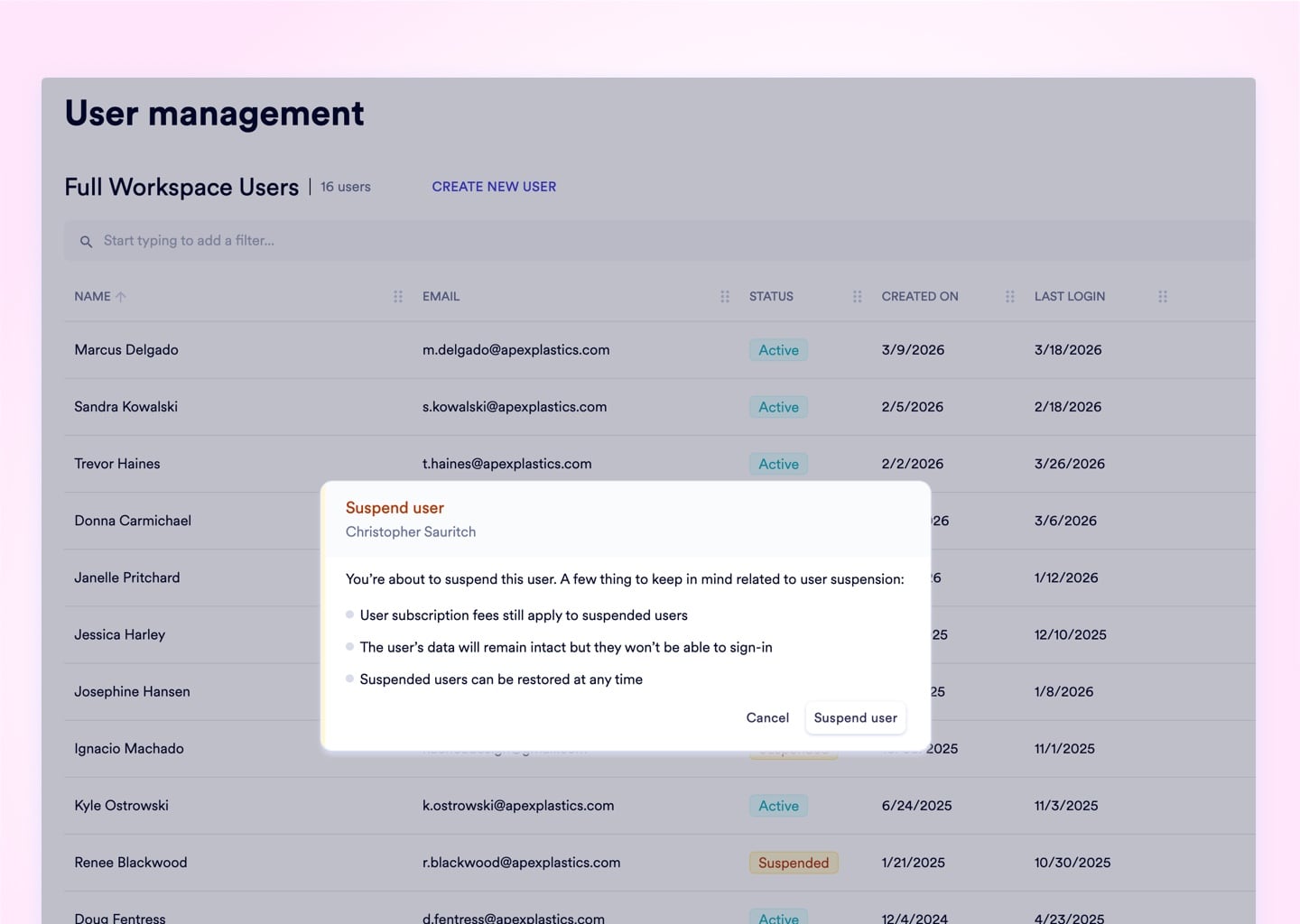
Instant Workforce Administration
Provision, update, or revoke any user seat in under 2 minutes. Monitor last sign-in telemetry, force 2FA compliance, and suspend terminated employees - all from a single admin panel with no IT involvement.
- Provision and deactivate accounts without IT tickets
- Force password resets from the admin console
- View last sign-in timestamps per user
- Bulk-manage cohorts via User Teams
- Suspend access instantly on employee termination
Zero-Cost External Access Provisioning
Provision auditors, 3PL contractors, and customers with highly restricted Guest accounts carrying auto-expiring credentials - separate security thresholds, zero billing impact, and no path to escalate internal permissions.
- Dedicated Guest role type with restricted defaults
- Auto-expiring invite links with configurable TTL
- Inactivity timeout stricter than internal employees
- Zero billing cost per Guest seat
- No Guest-to-internal permission escalation possible
Least-privilege access, enforced across all modules
Legacy ERPs were not designed for the principle of least privilege. They were designed for simplicity - and that simplicity is a security liability at scale. Naologic's architecture assumes no user should ever see data they don't need to perform their specific job function. Every role is an explicit configuration, not an inherited default. Every permission is a deliberate grant, not a broad category. Every data boundary - geographic, departmental, or document-level - is a hard system filter, not a policy suggestion. An Ohio plant manager cannot see Dallas margin data. A sales rep cannot edit another rep's quotes. A terminated employee loses system access in 90 seconds. The result is an environment where internal breaches and accidental data overwrites become structurally impossible, not just unlikely.
2-Factor Authentication
One compromised password cannot breach your entire ERP when 2FA is mandatory for all 50 users.
Naologic lets Super Admins mandate 2FA across the entire organization with one toggle - no user opt-outs, no exceptions. Both SMS and Authenticator Apps are supported. Non-compliant users are intercepted at login and forced through enrollment before accessing the workspace. For genuine emergencies - a lost device during a critical deal - 10 downloadable, single-use backup codes restore access without permanently disabling the 2FA layer.

Setup and Administration
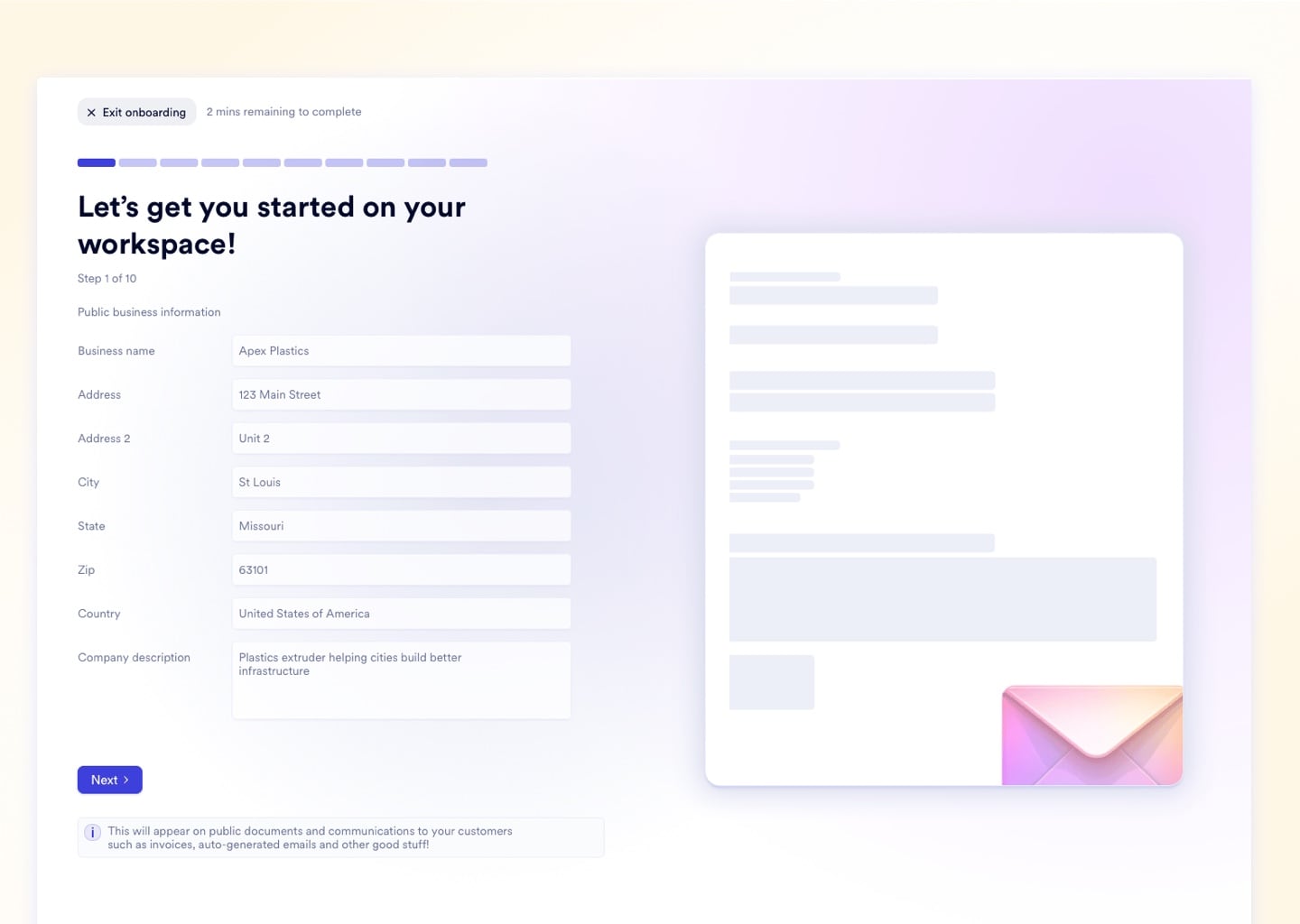
From First Login to Compliant Workspace in 4 Steps
Naologic's admin architecture is built for IT Directors who need complete access control without consulting fees or ticket queues. The Super Admin wizard initializes your security framework in a single session. Ongoing administration - provisioning, suspensions, role updates, Guest management - runs from the same console. No identity management tool. No database editor. No tickets.
Super Admin Initialization
Role Architecture Design
Seat Provisioning
Ongoing Governance and Monitoring
An unattended terminal on the production floor is a live data breach
An unattended terminal on the production floor is a live data breach. Naologic lets admins define exact idle timeout windows - not vague system defaults - and choose whether the session locks behind a PIN or terminates entirely. New user invitation links expire on your schedule: as short as one hour, up to one week. Guest accounts carry separate, more aggressive thresholds than internal employees. Set once. Enforced on every terminal, every shift.
Full Capability Index
Native Controls Spanning CRUD, Business Units, 2FA, and Audit Trails
Naologic's User and Role Management module covers the full lifecycle of digital access - from workspace initialization through day-to-day personnel changes to external audit provisioning. Every feature below is native to the platform, UI-driven, and requires zero database access, custom code, or consulting fees to configure.
The Four Failure Scenarios
Where Flat Permission Systems Create Liability
Manufacturers running QuickBooks or legacy ERPs rarely discover access control gaps until after an incident - a terminated employee accessing live accounts over the weekend, a junior buyer accidentally deleting a closed PO, or an external auditor handed a full Admin login because there was no restricted alternative. Naologic closes each of these gaps mechanically, not through policy.
The Terminated Employee Problem
A warehouse manager resigns Friday at 5 PM. IT tickets filed after hours sit unresolved until Monday morning - leaving active credentials and full system access for 48+ hours. In Naologic, the HR Director suspends the account from the admin console in under 90 seconds, terminating all active session tokens immediately.
The Multi-Plant Data Spillage Problem
A plant manager in Atlanta has no operational reason to view Chicago's open purchase orders, customer pricing, or margin reports. Business Units apply hard module filters - the Atlanta manager's views never return Chicago records, regardless of how they navigate the system.
The External Auditor Licensing Problem
An annual compliance audit requires your external CPA to review 6 months of financials. In NetSuite, that means purchasing a full-price enterprise license for a single engagement. In Naologic, it means a read-only Guest account with a 30-day auto-expiring credential - at zero additional cost.
The Shared Admin Login Problem
Three shift supervisors share a single "Admin" login because provisioning individual accounts requires an IT ticket and a full seat license. Every action is untraceable. Every accidental deletion is unattributable. Naologic removes both the cost barrier and the audit gap simultaneously.
The cost of flat permission systems, in numbers.
Inadequate access control doesn't just create security vulnerabilities - it generates administrative overhead, licensing costs, and audit exposure that accumulate every month. These four metrics represent the direct, measurable impact of replacing a flat permission system with Naologic's granular access architecture.
Naologic CRUD Control vs. QuickBooks, NetSuite, and Shared Logins
Most manufacturers have never had true granular access control - they have had workarounds. The table below maps Naologic's native access capabilities against the three most common status quo configurations in mid-market manufacturing.